ATVs, shot glasses, and baby furniture are part of this week's recall roundup
May 22, 2026
Recall Roundup
This roundup covers newly announced recalls and safety alerts from the U.S. Consumer Product Safety Commission and the Food and Drug Administration. The notices span childrens products, home goods, fitness gear, supplements and food sold nationwide.
Youth ATVs pose crash and burn risks
Lil Pick Up is recalling about 700 Sierra 125U youth ATVs because multiple safety failures can increase the risk of a crash, collision or severe burns.
- The ATVs can fail suspension, reverse-light, parking-brake and heat-surface safety requirements, creating serious crash and burn hazards.
- About 700 units were sold online and in stores from October 2025 through April 2026 for between $800 and $1,300.
- Consumers should stop using the youth ATVs immediately and contact Lil Pick Up for a full refund and free pickup.

Lil Pick Up Inc., of Rowland Heights, California, is recalling its Sierra 125U youth ATVs sold under various brand names, including Rider 9. The recalled vehicles have Sierra 125U on the VIN plate on the front frame column and a separate plate stating the ATV is subject to Lil Pick Ups CPSC-approved action plan. The youth ATVs were sold in red, blue, black, pink, gray, spider red and spider blue.
The hazard
The CPSC said the recalled youth ATVs violate the federal mandatory ATV safety standard and pose a risk of serious injury or death. According to the agency, the vehicles fail mechanical suspension requirements, the reverse indicator light does not illuminate, the parking brakes fail to hold, and surfaces near the footwell can become hot enough to cause severe burns. No incidents or injuries had been reported at the time of the recall.
What to do
Consumers should stop using the recalled youth ATVs immediately and contact Lil Pick Up for a full refund. The company said buyers will be asked to register for the recall at www.lilpickup.us and will then receive instructions on returning the ATV, including free pickup and transportation.
Company contact
Lil Pick Up can be reached collect at 951-245-5663 from 8 a.m. to 5 p.m. CT Monday through Friday, by email at contact@lilpickup.us, or online at www.lilpickup.us/recall-detail.html or www.lilpickup.us by clicking Recall at the top of the page.
Source
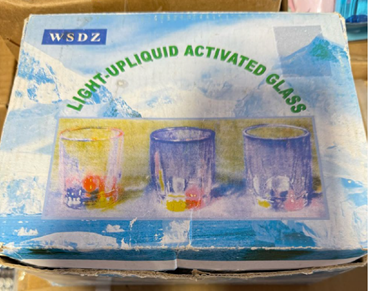
Light-up shot glasses expose button batteries
ABC Trading is recalling nearly 2,900 WSDZ-branded LED shot glasses because children can access the button cell batteries inside.
- The battery compartment can be opened too easily, creating a potentially deadly ingestion hazard for children.
- About 2,900 glasses were sold at gift stores nationwide from March 2024 through October 2025 for between $6 and $10.
- Consumers should stop using the glasses, keep them away from children, dispose of the batteries and request a full refund.
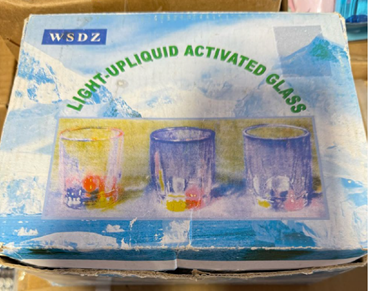
ABC Trading Inc., of Vernon, California, is recalling WSDZ-branded LED shot glasses sold individually and in packs of 24. The clear plastic glasses contain three button cell batteries that power LED lights when a push button on the underside is pressed. ITEM NO: LP-024 (122) and Importer: ABC Trading, Inc are printed on a label on the underside.
The hazard
The CPSC said the glasses violate the mandatory standard for consumer products with button cell and coin batteries because children can easily access the batteries. The packaging and product also lack the warnings required under Reeses Law. If swallowed, button cell or coin batteries can cause internal chemical burns, serious injuries and death. No incidents or injuries had been reported.
What to do
Consumers should stop using the recalled glasses immediately, place them where children cannot reach them and properly dispose of the batteries. ABC Trading said consumers can obtain a full refund by disposing of the glass, taking a photo of the product in the trash and emailing the image to recallabc@gmail.com.
Company contact
ABC Trading can be reached toll-free at 323-581-3688 from 9:30 a.m. to 6 p.m. PT Monday through Friday, by email at recallabc@gmail.com, or online at https://www.abctradinginc.com/recall-2 or www.abctradinginc.com by clicking Recall Information at the top of the page.
Source
Hook-on chairs create deadly fall hazard
PandaEar is recalling about 9,700 portable hook-on chairs because a removable crotch restraint can allow infants to fall through an opening.
- The crotch restraint can be removed without a tool, creating a deadly fall hazard for infants and toddlers.
- About 9,700 chairs were sold on Amazon.com from February 2022 through November 2025 for about $25.
- Consumers should stop using the chairs immediately, destroy the seating components as directed and request a full refund.

PandaEar, of Lake Dallas, Texas, and Rockville, Maryland, is recalling two models of portable hook-on chairs used to seat young children at a dining table. The chairs have a black or gray metal frame, fabric seats in black, gray or blue dinosaur print, and two metal arms with plastic covers that anchor the seat to the table. Panda Ear appears on a label stitched to the side of the seat, while model C2102 is listed on a label on the bottom of the fabric seat; model BTC-51 has no product markings.
The hazard
The recalled chairs violate the mandatory federal standard for portable hook-on chairs, according to the CPSC. The agency said the crotch restraints can be removed without the use of a tool, allowing infants to fall through an opening in the seat and suffer serious or fatal injuries. No incidents or injuries had been reported.
What to do
Consumers should stop using the recalled hook-on chairs immediately and contact PandaEar to receive a full refund. The company said consumers will be asked to disassemble the chair, cut the restraint straps and fabric seat, and email photographs showing the destroyed product and model label to pandaear_recall@outlook.com.
Company contact
PandaEar is handling the recall by email only at pandaear_recall@outlook.com.
Source
Resistance bands can snap off handles
HomeProGym is recalling certain resistance bands after reports that the bands can forcefully separate from the handle during workouts.
- The purple 60-pound and gray 70-pound bands can detach from the handle and strike users.
- About 700 recalled bands were sold as part of bundled sets on Homeprogym.com and Amazon.com from December 2025 through April 2026.
- Consumers should stop using the affected bands immediately and contact HomeProGym for a refund or store credit.

Supa Products Pte Ltd., doing business as HomeProGym in Singapore, is recalling HomeProGym-branded resistance bands sold in multiple stackable fitness sets and bundles. Only the purple 60-pound resistance band and the gray 70-pound resistance band are included in the recall. The latex bands have a silver metal D-ring at each end attached to a black strap, with HOME PRO GYM and either ULTRA or ULTRA PLUS printed on the strap.
The hazard
The CPSC said the recalled resistance bands can forcefully separate from the handle during use, posing a serious impact hazard. HomeProGym said it had received five reports of bands separating from the handle. No injuries had been reported.
What to do
Consumers should stop using the recalled purple 60-pound and gray 70-pound bands immediately and contact HomeProGym for either a full refund or a $50 HomeProGym.com store credit. The company said consumers should cut the recalled bands in half, send a photo of the destroyed bands to support@homeprogym.com and complete the registration form at https://homeprogym.com/pages/recall. The other bands in the sets can continue to be used.
Company contact
HomeProGym can be reached by email at support@homeprogym.com or online at https://homeprogym.com/pages/recall or https://homeprogym.com/ by clicking on Safety Recalls at the bottom of the page.
Source
Childrens toys expose deadly button batteries
ABC Trading is recalling more than 84,000 childrens toys because battery compartments can be opened by children, creating a deadly ingestion risk.
- The recalled toy headbands and electronic pet cages contain accessible button cell batteries that can cause fatal internal burns if swallowed.
- About 84,700 toys were sold at TOYZ and Joissu Product stores nationwide from November 2022 through October 2025 for between $5 and $9.
- Consumers should stop using the toys immediately, dispose of them and contact ABC Trading for a full refund.

ABC Trading Inc., of Vernon, California, is recalling several battery-powered childrens toys, including a pink bow toy headband, model 6300RP, and electronic pet cage toys, models 8266 (ZH998-22) and ZH998-23. The headband has a push button that lights up the bow, while the pet cage toys include a silver cage with a red dinosaur and yellow egg or a pink cage containing a blue bird. Regulators said children can access the batteries too easily.
The hazard
The CPSC said the toys violate the mandatory federal standard for toys because the button cell battery compartments can be opened by children. If swallowed, button cell and coin batteries can cause internal chemical burns, serious injury and death. No incidents or injuries had been reported.
What to do
Consumers should stop using the recalled toys immediately and contact ABC Trading for a refund. The company said consumers will be asked to dispose of the products, take a photo showing them in the trash and email the image to recallabc@gmail.com to receive a full refund of the retail price.
Company contact
ABC Trading can be reached toll-free at 323-581-3688 from 9:30 a.m. to 6 p.m. PT Monday through Friday, by email at recallabc@gmail.com, or online at https://www.abctradinginc.com/recall-2 or www.abctradinginc.com by clicking Recall Information at the top of the page.
Source
Illuminated ribbon spheres may overheat
Bethlehem Lights is recalling 10-inch Illuminated Ribbon Spheres sold by QVC after reports of sparking and overheating.
- The LED lights inside the decorative sphere can overheat and create a fire hazard.
- About 2,000 units were sold on QVC.com from July 2024 through April 2026 for about $43.
- Consumers should unplug the product immediately, cut the power cord and contact Bethlehem Lights for a refund.

Bethlehem Lights LLC, of Naperville, Illinois, is recalling its 10-inch Illuminated Ribbon Sphere, a silver-toned spherical ornament with a spiral faceted design and warm-white LED lights inside. The product was sold online by QVC. The company said the decorative sphere can overheat during use.
The hazard
The recalled LED lights can overheat, posing a risk of serious injury or death from fire, according to the CPSC. Bethlehem Lights said it had received nine reports of the product sparking or overheating. No injuries had been reported.
What to do
Consumers should stop using the recalled illuminated spheres immediately, unplug them from the wall and cut the power cord. To receive a full refund, Bethlehem Lights said consumers should email a photo of the product showing the cut cord to ribbonsphere@bethlehemlights.com before disposing of it in the garbage.
Company contact
Bethlehem Lights LLC can be reached toll-free at 877-661-8324 from 8 a.m. to 5 p.m. CT Monday through Friday, by email at ribbonsphere@bethlehemlights.com, or through https://www.qvc.com/ by clicking Product Recall Info at the bottom of the page.
Source
Squeeze toys may contain asbestos
The Orb Factory is recalling more than 121,000 Orb Funkee squeeze toys because the sand filling may contain tremolite asbestos.
- The sand inside the toys may contain fibrous tremolite, and inhaling asbestos can cause serious health problems.
- About 121,340 toys were sold at Walmart and Ollies Bargain Outlet stores nationwide from February 2025 through April 2026.
- Consumers should take the toys away from children, stop using them and contact The Orb Factory for a refund.

The Orb Factory Limited, doing business as ORB Toys in Canada, is recalling two models of Orb Funkee squeeze toys with date code 3102491A. The products are soft, stretchable toys filled with sand and include model 17451, a large golden monkey, and model 41929, assorted smaller monkees in colors such as orange, purple and green. The date code is printed on the hand of the large toy or on the back of the smaller toys.
The hazard
The CPSC said the recalled squeeze toys may contain fibrous tremolite, a form of asbestos, in the sand filling. Exposure to asbestos fibers can cause adverse health effects if the fibers are inhaled. No incidents or injuries had been reported at the time of the recall.
What to do
Consumers should immediately take the recalled toys away from children, stop using them and contact The Orb Factory for a refund. The company said consumers should verify the code and lot number, place the toy in a heavy-duty plastic bag, seal it securely with tape and email a photo of the bagged toy to customerservice@orbtoys.com. If a toy has ruptured or leaked sand, the company directed consumers to wear a mask and gloves, use damp cloths to collect the material, double-bag the toy and cleanup materials, and dispose of the sealed bags according to local or state regulations.
Company contact
The Orb Factory can be reached at 800-741-0089 from 8 a.m. to 4 p.m. ET Monday through Friday, by email at customerservice@orbtoys.com, or online at www.orbtoys.com by clicking RECALL INFORMATION at the bottom of the page.
Source
Pancake mix may contain undeclared egg
Hometown Food Company has issued an allergy alert for Birch Benders 12 oz Sweet Potato Pancake and Waffle Mix because some packages may contain undeclared egg.
- The mix may contain egg that is not listed on the label, creating a serious allergy risk for sensitive consumers.
- The product was distributed nationwide through grocery stores, natural food retailers and online channels.
- Consumers should discard the affected mix immediately or return it to the store where it was purchased for a refund.

Hometown Food Company is recalling Birch Benders 12 oz Sweet Potato Pancake and Waffle Mix after discovering that some product may contain undeclared egg. The affected item carries case item code 8 1000156076 5, UPC item code 8 1000156076 8, lot code 5 265 and a best-if-used-by date of March 24, 2027. The product was distributed nationwide.
The hazard
For people with an allergy or severe sensitivity to egg, eating the recalled pancake and waffle mix could trigger a serious or life-threatening allergic reaction. The FDA notice did not list any illnesses.
What to do
Consumers who purchased the affected Birch Benders mix should not eat it. Hometown Food Company said the product should be discarded immediately or returned to the retail location where it was purchased for a refund.
Company contact
Consumers with questions can call 1-855-206-9517.
Source
Minestrone soup may contain undeclared shrimp
Kettle Cuisine has issued an allergy alert for Whole Foods Market Kitchen Minestrone Soup because some containers may contain undeclared shrimp.
- The soup may contain shrimp not disclosed on the label, creating a potentially life-threatening shellfish allergy risk.
- The affected soup was sold in Whole Foods stores in 18 states and online through Whole Foods and Amazon.
- Consumers should return the affected product to the place of purchase for a full refund.

Kettle Cuisine is recalling Whole Foods Market Kitchen Minestrone Soup because the product may contain undeclared shrimp. The affected containers have lot code 1762181, a use-by date of 05/27/26 printed on the top rim of the cup, and UPC 099482502065 on the back label. Distribution included Whole Foods retail stores in AL, CT, DC, FL, GA, MA, MD, ME, MS, NC, NH, NJ, NY, PA, RI, SC, TN and VA, along with nationwide online sales through Whole Foods and Amazon.
The hazard
People who are allergic to crustacean shellfish, including shrimp, could face a serious or life-threatening allergic reaction if they consume the recalled soup. The FDA alert did not list any illnesses.
What to do
Consumers who purchased the affected soup should not eat it. Kettle Cuisine said buyers should return the product to the place of purchase for a full refund.
Company contact
Consumers with questions can call 617-409-1100 Monday through Friday from 8 a.m. to 5 p.m. ET.
Source
Sex enhancement capsules contain hidden drugs
Best Supplements Best Prices is recalling WAP Sensual Enhancement Capsules because the capsules contain undeclared prescription drug ingredients.
- The capsules contain undeclared sildenafil, tadalafil and flibanserin, which can dangerously interact with other medications and alcohol.
- All lots with UPC 80174 00462 were distributed nationwide in the U.S. through eBay.
- Consumers should stop using the capsules immediately, dispose of them and contact the firm for a refund.

Best Supplements Best Prices has issued a voluntary nationwide recall of WAP Sensual Enhancement Capsules sold online through www.ebay.com. The recall covers all lots of the product with UPC 80174 00462. The company said customers are being notified by email and offered full refunds.
The hazard
The FDA said the capsules contain undeclared sildenafil, tadalafil and flibanserin. Sildenafil and tadalafil can interact with nitrates found in some prescription drugs, such as nitroglycerin, and may cause blood pressure to drop to dangerous levels. Flibanserin can cause drowsiness, sedation, fainting and dangerously low blood pressure, especially when combined with alcohol. Consumers with diabetes, high blood pressure, high cholesterol or heart disease may face elevated risk because they are more likely to take nitrates.
What to do
Consumers who have WAP Sensual Enhancement Capsules should stop using the product immediately and dispose of it. Best Supplements Best Prices said it is arranging full refunds for recalled products and is notifying customers by email.
Company contact
Consumers can contact the company by email at eroticenhancers@gmail.com or by calling 818-856-2141.
Source
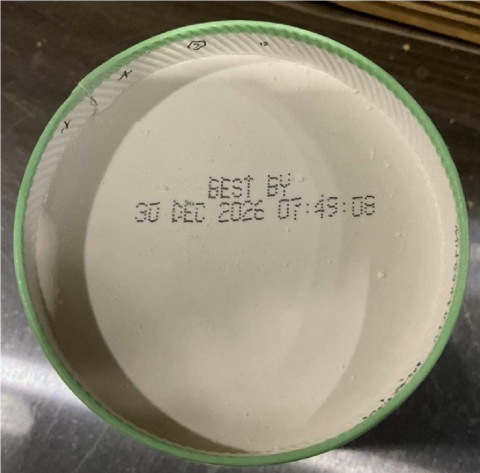
Tahina recalled over Salmonella contamination
Nassar Investments is recalling Malazi Tahina after the product was found to be contaminated with Salmonella.
- The recalled tahina may contain Salmonella, which can cause severe illness and can be especially dangerous for vulnerable people.
- The product was sold in plastic bottles in Michigan and North Carolina between March 1, 2025, and June 9, 2025.
- Consumers should not eat the tahina and should discard the product immediately.

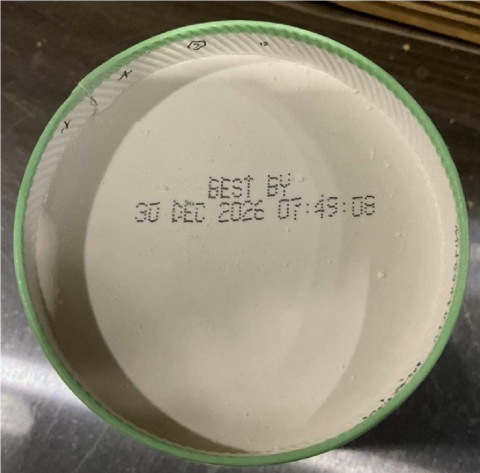
Nassar Investments is recalling Malazi Tahina due to Salmonella contamination. The recalled product has UPC 6 224011 088244 and expiration date 30/12/2026. According to the FDA notice, the tahina was distributed in retail stores in Michigan and North Carolina.
The hazard
Salmonella can cause serious and sometimes fatal infections in young children, frail or elderly people and others with weakened immune systems. Healthy people may experience fever, severe headache, stiffness, nausea, abdominal pain and diarrhea, while pregnant women can face risks including miscarriage and stillbirth. The FDA notice did not mention any illnesses.
What to do
Consumers who purchased the recalled tahina should not consume it and should discard the product. Anyone who believes they may have become ill should contact a health care provider.
Company contact
Consumers can contact Mr. Akram Nassar at 919-949-3534.
Source
Kroger croutons face Salmonella risk
Sugar Foods LLC is recalling specific lots of Kroger Homestyle Cheese Garlic Croutons because of potential Salmonella contamination.
- The recalled croutons may be contaminated with Salmonella, which can cause serious illness in children, older adults and people with weakened immune systems.
- The affected lots were sold at Kroger stores in 17 states and carry UPC 0 11110 81353 4 with select best-if-used-by dates.
- Consumers should check the UPC and best-if-used-by dates and contact Sugar Foods LLC directly for questions or more information.

Sugar Foods LLC has issued a supplier-initiated recall of specific lots of Kroger Homestyle Cheese Garlic Croutons. The affected product bears UPC 0 11110 81353 4 and best-if-used-by dates from Feb. 17, 2027, through April 7, 2027, including multiple dates listed in the recall notice. The croutons were sold at Kroger stores in AL, AR, GA, IL, IN, KY, LA, MI, MO, MS, OH, SC, TN, TX, VA, WI and WV.
The hazard
Salmonella can cause serious and sometimes fatal infections in young children, frail or elderly people and others with weakened immune systems. Healthy people can experience fever, diarrhea, nausea, vomiting and abdominal pain, and in rare cases the infection can spread to the bloodstream and cause more serious conditions such as arterial infections, endocarditis and arthritis. The FDA notice did not list any illnesses.
What to do
Consumers should check whether their package matches the recalled UPC and one of the listed best-if-used-by dates. Sugar Foods LLC said consumers who purchased one of the recalled lots may contact the company directly at 332-240-6676 for questions or more information.
Company contact
Consumers can call Sugar Foods LLC at 332-240-6676. Media inquiries can be directed to Ms. Krista Locke at 805-396-5000.
Source
Organic ice cream may contain metal
Straus Family Creamery is recalling select flavors of its Organic Super Premium Ice Cream because the products may contain metal fragments.
- The recalled ice cream may contain metal foreign material, creating a potential choking or injury hazard.
- The affected products were distributed in 17 states and carry listed best-by dates in late December 2026.
- Consumers should not eat the ice cream and should discard it, then visit the companys recall page for a replacement voucher.
Straus Family Creamery is voluntarily recalling select flavors of Organic Super Premium Ice Cream due to the potential presence of metal fragments. The recall covers products with best-by dates of Dec. 23, 24, 25, 26, 27, 28 and 30, 2026. The affected ice cream was distributed in Arizona, California, Colorado, Connecticut, Florida, Georgia, Iowa, Illinois, Indiana, Maryland, New Jersey, Oregon, Pennsylvania, South Carolina, Texas, Washington and Wisconsin.
The hazard
The recall was issued because the ice cream may contain metal foreign material. The FDA notice did not provide injury reports, but metal fragments in food can present a risk of injury if consumed.
What to do
Consumers who purchased the recalled ice cream should not eat it and should discard it. Straus Family Creamery said consumers should not return the product to the store. Those seeking a voucher for a replacement product can visit https://www.strausfamilycreamery.com/recall/.
Company contact
Straus Family Creamery can be reached at support@strausmilk.com or 1-707-776-2887 Monday through Friday from 9:30 a.m. to 5 p.m. PT.
Source
Seasoning recalled over possible Salmonella risk
Blackstone Products is recalling Parmesan Ranch seasoning sold at Walmart and on its website because of possible Salmonella contamination.
- The seasoning may be contaminated with Salmonella, which can lead to severe illness and bloodstream infections in rare cases.
- The recall covers lot codes 2025-43282, 2025-46172 and 2026-54751 sold nationwide through Walmart and Blackstone Products.
- Consumers should not consume the seasoning, should dispose of it immediately and may contact the company for a replacement.

Blackstone Products is voluntarily recalling Parmesan Ranch seasoning because of a potential foodborne illness risk tied to Salmonella. The affected lots are 2025-43282, 2025-46172 and 2026-54751. The seasoning was sold nationwide exclusively through Walmart stores and through the Blackstone Products website.
The hazard
Salmonella can cause serious and sometimes fatal infections in young children, frail or elderly people and others with weakened immune systems. Healthy people commonly experience fever, diarrhea, nausea, vomiting and abdominal pain, and in rare cases the infection can enter the bloodstream and cause more severe illnesses such as infected aneurysms, endocarditis and arthritis. The FDA notice did not mention any illnesses.
What to do
Consumers who have the affected seasoning should not consume it and should dispose of it immediately. Blackstone Products said customers who purchased one of the affected products may contact the company directly to obtain a replacement product.
Company contact
Consumers can call 1-888-879-4610. Media inquiries can be directed to Tracy Baldwin at 435-252-3030 or tbaldwin@weberblackstone.com.
Source